How to Install Ubuntu on Windows 10 Using Windows Subsystem for Linux (WSL)
Windows Subsystem for Linux (WSL) allows you to run a real Linux environment directly on Windows—no virtual machines, no dual boot. This is incredibly useful for developers, DevOps engineers, cybersecurity…
The Pain of Untapped Potential: Why Knowing Your Ability Without Action Hurts the Most
One of the greatest pains a person can experience is recognizing their potential but failing to fully utilize or execute it. It’s not the absence of talent or opportunity that…
The Quiet Truth About Confidence: Why the Loudest People Are Often the Most Insecure
One idea from Adlerian psychology struck me recently because of how accurately it describes human behavior — especially in our online world. It’s this: If a person truly has confidence…
The Hidden Power of Weakness: What Adler Taught Me About Strength
Recently, I’ve been diving deeper into psychology, and I’ll be honest — it’s both eye-opening and uncomfortable. The more I learn, the more I realize how much of our lives…
How Chinese Hackers Unleashed AI to Automate a Global Cyber Espionage Attack
In a major turning point for cybersecurity, researchers have confirmed that state-sponsored hackers from China used AI technology to carry out a large-scale cyber espionage campaign with minimal human involvement.…
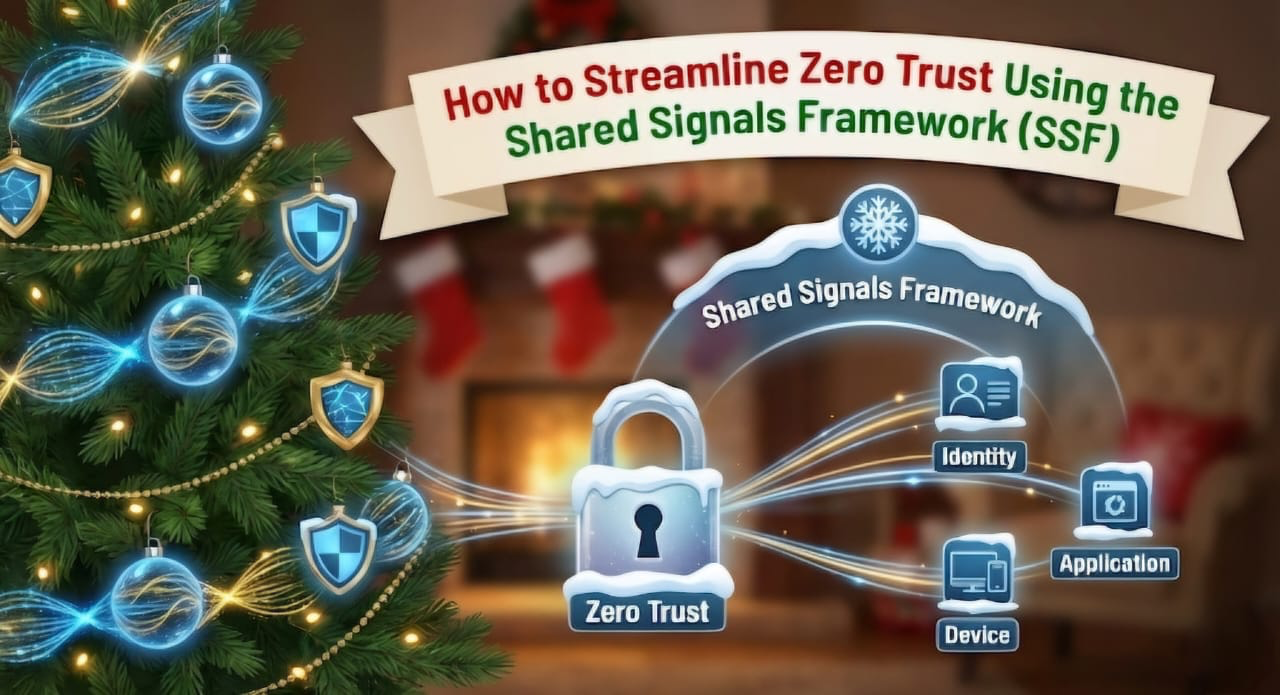
How to Streamline Zero Trust Using the Shared Signals Framework (SSF)
Zero Trust security is designed to reduce attack surfaces and enable faster threat response. But in reality, many organizations struggle to implement it effectively—not because they lack tools, but because…
How Retailers Can Prepare for the Most Dangerous Cyber Season of the Year
The holiday season may be the most profitable time for retailers—but it’s also the most dangerous from a cybersecurity perspective. As shopping traffic spikes, attackers take advantage of overloaded systems,…
New Malware Campaign Alert: JS#SMUGGLER Is Using Compromised Websites to Spread NetSupport RAT
Cybersecurity researchers have uncovered a new web-based malware campaign called JS#SMUGGLER, which uses hacked websites to secretly infect users with a powerful remote access trojan known as NetSupport RAT. According…
“It Wasn’t Me, It Was My Vendor”: Why Supply Chain Attacks Are Your Newest Headache
You do everything right. You use strong, unique passwords. You have multi-factor authentication enabled. Your phone software is up to date. Yet, one day you get a notification: your data…
The New Face of Scams: How AI is Supercharging Phishing
Phishing scams, the deceptive practice of using fake emails or messages to trick individuals into revealing sensitive information, have taken on a new, more sophisticated form with the integration of…