How to Free Up Disk Space Without Deleting Important Files
Running out of disk space is one of the most frustrating computer problems. That dreaded “Low Disk Space” warning appears, your system slows to a crawl, and you’re left wondering…
How to Speed Up a Slow Laptop Without Buying a New One
Is your laptop running slower than molasses? Before you start shopping for a replacement, there’s good news: you can often restore your laptop’s performance without spending a fortune on a…
Why Deleted Files Aren’t Really Gone (And How to Recover Them)
I used to believe that once a file was deleted, it was gone for good.Empty the Recycle Bin? Gone.Format the drive? Completely erased.End of story. For a long time, that…
How to Explain What You Do for a Living (Without Confusing People)
At some point, almost everyone gets asked this simple question: “So… what do you do for a living?” For many professionals—especially in technical or specialized fields—this question can feel oddly…
What Really Separates Senior Engineers from Juniors?
Many people say coding and programming are hard—and they’re right. But after years of building production systems, I’ve learned that something is even harder than writing code or deploying applications.…
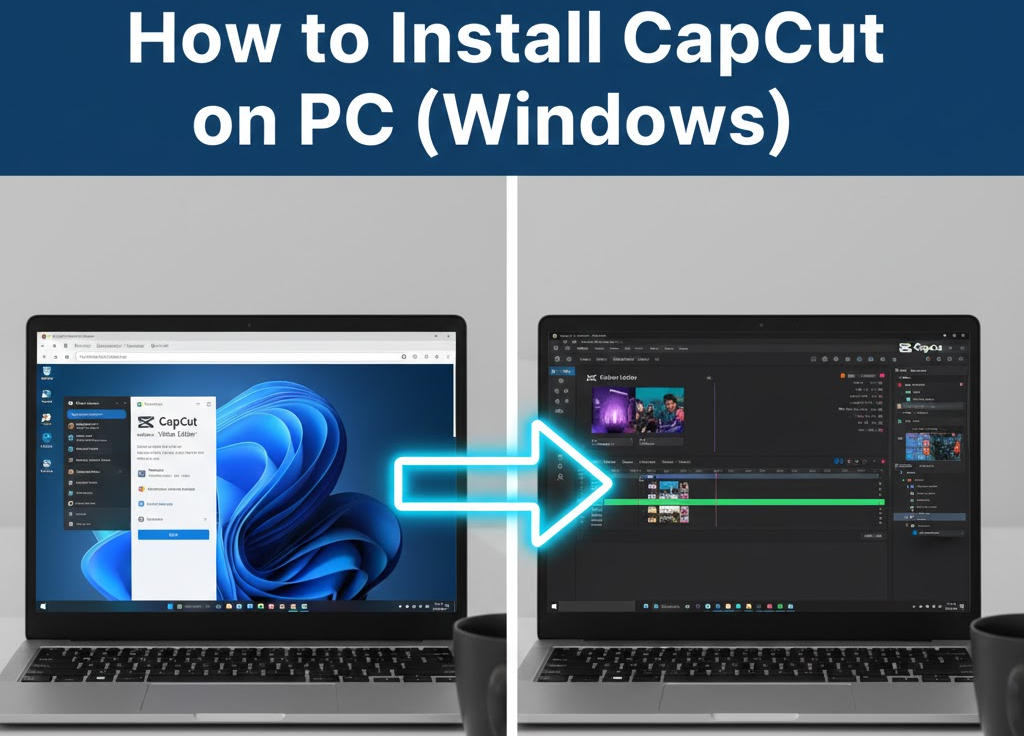
How to Install CapCut on PC (Windows 10 & Windows 11)
CapCut is one of the most popular video editing tools today, especially for content creators on YouTube, TikTok, Instagram, and Facebook. While many people know CapCut as a mobile app,…
How to Install Ubuntu on Windows 10 Using Windows Subsystem for Linux (WSL)
Windows Subsystem for Linux (WSL) allows you to run a real Linux environment directly on Windows—no virtual machines, no dual boot. This is incredibly useful for developers, DevOps engineers, cybersecurity…
The Pain of Untapped Potential: Why Knowing Your Ability Without Action Hurts the Most
One of the greatest pains a person can experience is recognizing their potential but failing to fully utilize or execute it. It’s not the absence of talent or opportunity that…
The Quiet Truth About Confidence: Why the Loudest People Are Often the Most Insecure
One idea from Adlerian psychology struck me recently because of how accurately it describes human behavior — especially in our online world. It’s this: If a person truly has confidence…
The Hidden Power of Weakness: What Adler Taught Me About Strength
Recently, I’ve been diving deeper into psychology, and I’ll be honest — it’s both eye-opening and uncomfortable. The more I learn, the more I realize how much of our lives…