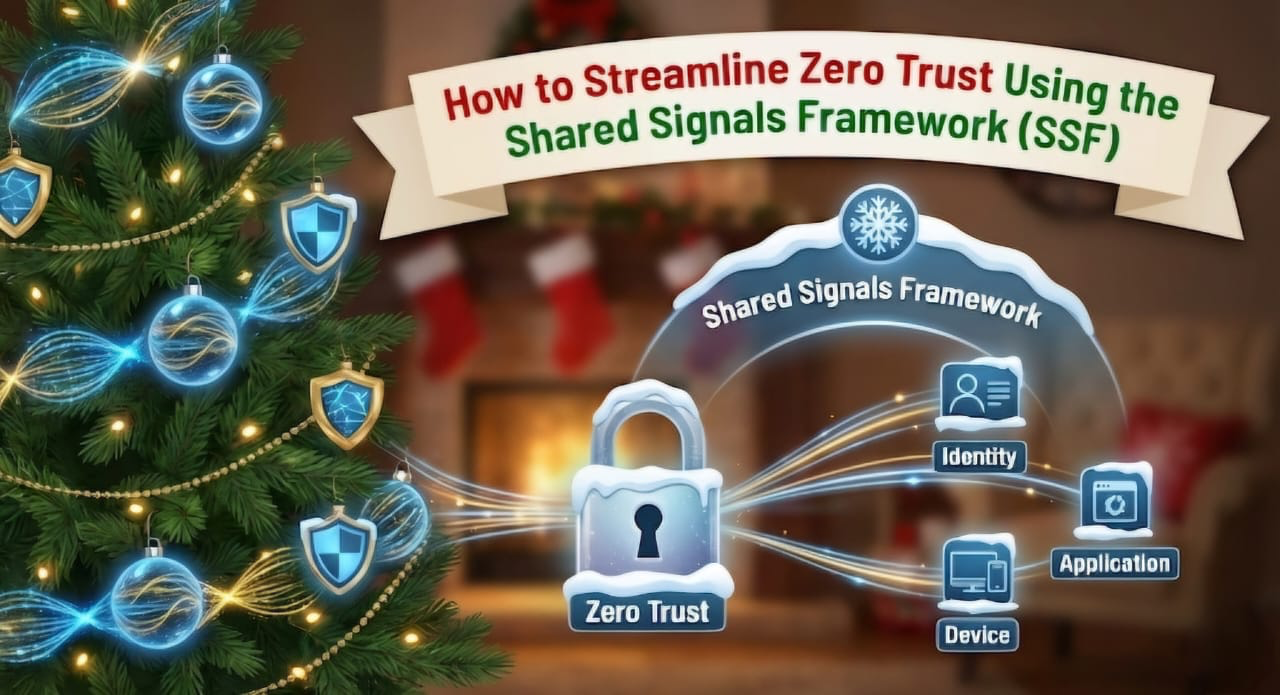
Zero Trust security is designed to reduce attack surfaces and enable faster threat response. But in reality, many organizations struggle to implement it effectively—not because they lack tools, but because their security tools don’t communicate well with each other. In fact, research shows that a large majority of organizations face serious challenges when trying to deploy Zero Trust due to poor signal sharing between platforms.
That’s where the Shared Signals Framework (SSF) comes in.
SSF provides a standardized method for exchanging real-time security events between different systems. In theory, this allows identity platforms, endpoint security tools, and access control systems to work together. In practice, adoption is uneven, and many popular tools still don’t support SSF natively—creating gaps in Zero Trust enforcement.
The Core Problem
Zero Trust depends on continuous awareness of device and user risk. But organizations often face three major roadblocks:
- Many IAM and endpoint tools don’t support SSF
- Security signals often require extra enrichment and correlation
- Managing SSF endpoints and cryptographic tokens adds engineering overhead
This lack of interoperability means that critical device risk events may never reach identity systems like Okta—allowing risky devices to retain access longer than they should.
The Breakthrough Solution
A Senior IAM Engineer at MongoDB proposed a practical workaround by building a workflow that bridges non-SSF tools into SSF-compatible systems using automation.
By combining:
- Kolide (device trust monitoring)
- Tines (workflow automation)
- Okta (identity and access management)
The system converts raw device compliance issues into standardized Shared Signals Framework (CAEP) events that Okta can instantly act on.
Here’s what happens in real time:
- Kolide detects a device that becomes non-compliant
- A webhook sends the alert to Tines
- Tines enriches the signal, maps the device to a user, and builds a Security Event Token (SET)
- The SET is signed and sent to Okta
- Okta immediately updates access policies based on the new risk level
This allows Zero Trust enforcement to happen automatically and instantly, even when tools don’t natively support SSF.
Why This Matters
This approach enables:
- Real-time device risk visibility
- Faster and automated access revocation
- Better policy enforcement
- Less manual security intervention
- Stronger Zero Trust posture without adding friction to users
Instead of waiting for vendors to fully support SSF, organizations can now use automation to close the Zero Trust gap today.
Final Takeaway
Zero Trust only works when security signals move freely across systems. The Shared Signals Framework provides the standard—but automation platforms like Tines make it practical in real-world environments, even when vendors lag behind.
This is a powerful example of how security architecture and workflow automation can solve real enterprise security bottlenecks.
Source:
https://thehackernews.com/2025/12/how-to-streamline-zero-trust-using.html
More Articles Like This